Track every device.
Prove every destruction.
Serial-number level tracking from pickup to destruction. Download certificates, run audit reports, and demonstrate compliance — all from one dashboard.
- Serial number tracking for every device
- Real-time destruction status updates
- Downloadable certificates of destruction
- Audit-ready compliance reports
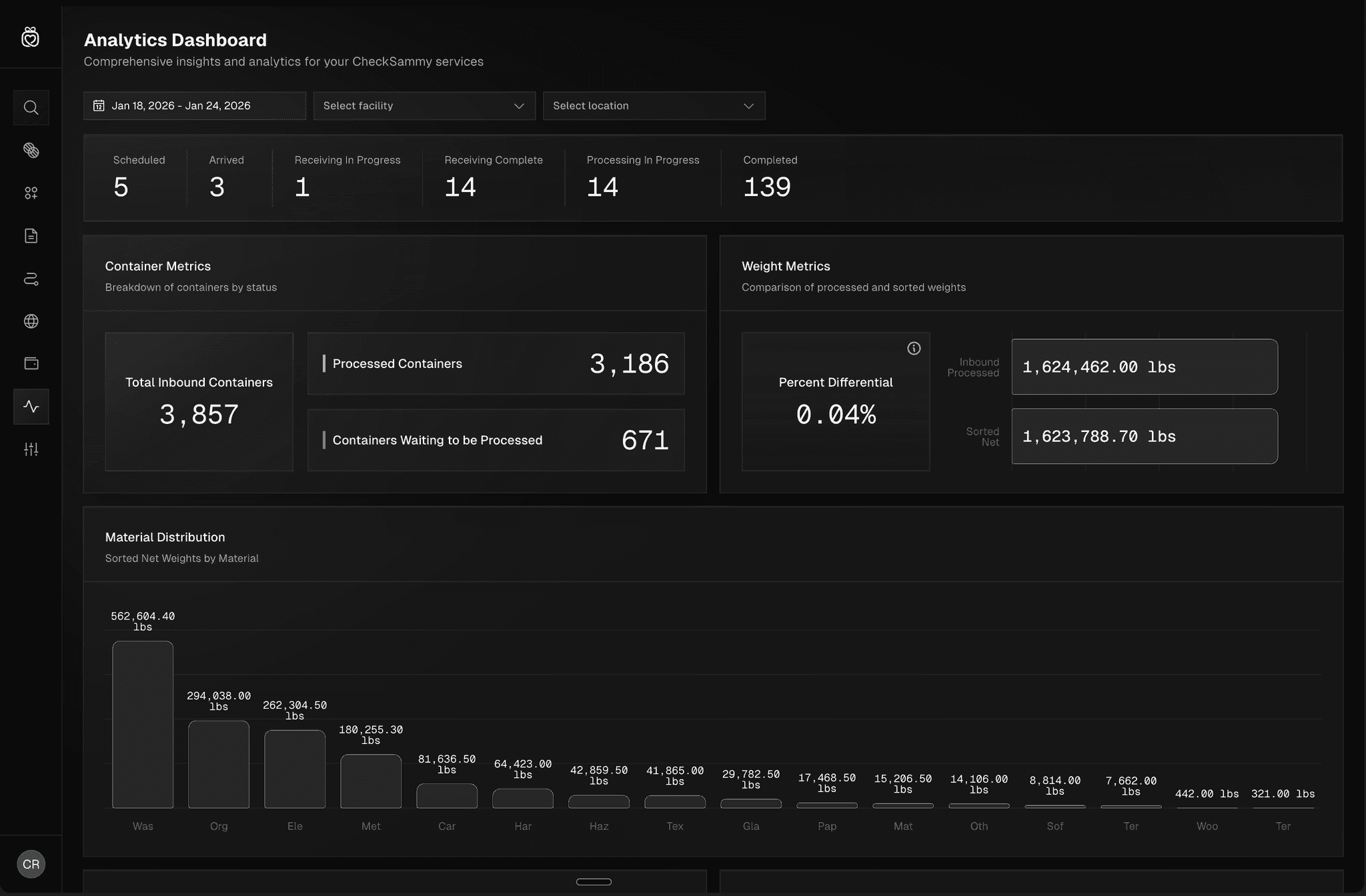
Serial-level asset tracking and destruction verification